How AI Is Reshaping Trust and Defense
Artificial intelligence is creating a new security paradox. The same technology that helps organizations detect threats faster is also expanding the attack surface, accelerating phishing, enabling more convincing synthetic media, and creating new risks around models, data, and automation pipelines.
Deloitte frames this tension directly in Tech Trends 2026, arguing that AI is becoming both a tool for cyber defense and a target that must be secured.
That is why two ideas are moving to the center of the technology conversation. The first is preemptive cybersecurity: using AI to anticipate, prioritize, and disrupt threats before they become full incidents. The second is digital provenance: building systems that can verify where digital content came from. Together, these ideas speak to the same challenge: in an AI-heavy internet, defense has to become proactive, and trust has to become verifiable.
Why Cybersecurity Is Moving From Reactive to Preemptive
Traditional cybersecurity has often been reactive. Teams investigate alerts, respond to incidents, patch known vulnerabilities, and try to reduce damage after a breach begins. That model is increasingly strained by the volume, speed, and complexity of modern threats.

Machine-Speed Defense
Preemptive cybersecurity means using AI systems to surface weak signals earlier, correlate events across massive datasets, identify likely attack paths, and automate parts of investigation and containment.
Microsoft’s Security Copilot positioning reflects that shift: describing AI agents that shrink response time, improve prioritization, and support continuous analysis at machine speed.
[ SECURITY_OPERATIONS_SIMULATOR ]
Compare the operational timeline of traditional response versus preemptive AI defense.
Why Digital Provenance Matters Now
At the same time, AI has created a second crisis: a trust crisis. As image, audio, video, and text generation improve, it becomes harder to know whether a file is original, edited, synthetic, or miscontextualized.
The C2PA explains provenance as the recorded history of a piece of digital content from creation through subsequent modifications. Its Content Credentials framework is designed to express that history in a cryptographically secure way.
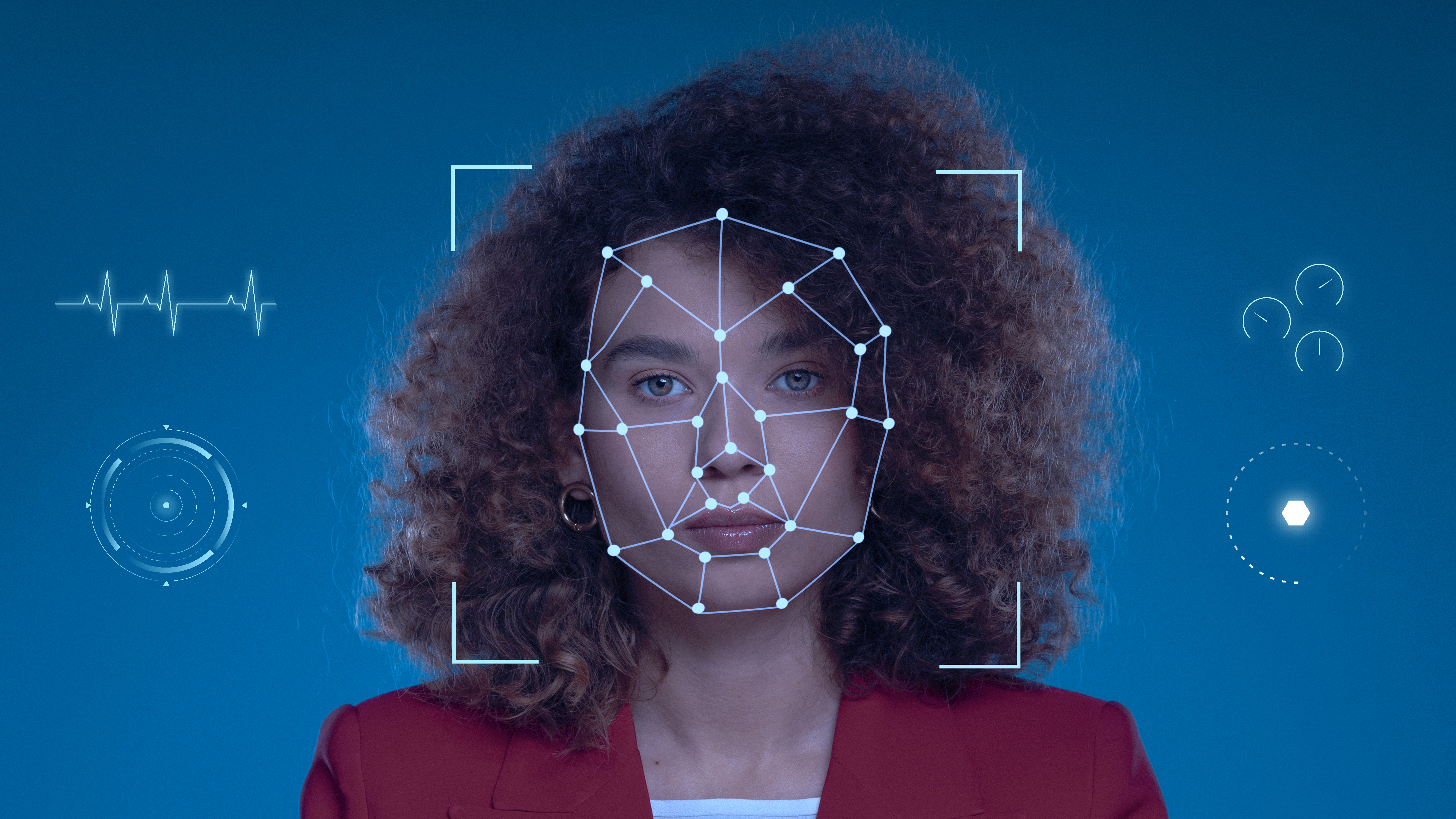
Content Credentials Inspector
Verify cryptographic history instead of guessing visual realism.

Why Watermarking Helps, But Is Not Enough
Watermarking (SynthID)
Tools like Google DeepMind's SynthID embed invisible marks in content to help identify AI generation.
A Layered Problem
NIST frames the problem as layered: provenance tracking, labeling, watermarking, detection, and governance all matter.
The strong version of the argument is not "watermarking solves deepfakes." It is "watermarking can improve transparency when paired with provenance, detection, and broader platform policies." Detection is probabilistic; provenance is evidentiary when it exists and is preserved.
Why This Matters for Business
For enterprises, the combination of preemptive cybersecurity and digital provenance is strategically important because both are about resilience under AI pressure. Cyber teams need defenses that act earlier and scale better.
Media teams, platforms, and brands need ways to prove authenticity and reduce reputational risk in a world of manipulated content. These are not separate problems anymore. AI connects them. Google Cloud, Microsoft, Deloitte, NIST, and Adobe all point to the same broad reality: security and trust are both being rebuilt for the AI era.
Frequently Asked Questions
It is the use of forward-looking defense methods, often powered by AI, to identify, prioritize, and mitigate threats earlier rather than waiting for full incidents to unfold.
The recorded history of a digital asset. C2PA's Content Credentials provide a cryptographically secure way to capture and express that provenance.
No. Content Credentials record provenance in a cryptographically bound structure, while watermarking marks content directly to help identify AI generation.
No. NIST presents synthetic content risk reduction as a multi-layered challenge involving provenance, labeling, detection, and governance, as detection alone is probabilistic.
>> Bibliographic_References.log
- [01] Deloitte. Tech Trends 2026 and The AI dilemma: Securing and leveraging AI for cyber defense.
- [02] Google Cloud. Cybersecurity Forecast 2026.
- [03] Microsoft. Security Copilot and related agent announcements.
- [04] NIST. Reducing Risks Posed by Synthetic Content: An Overview of Technical Approaches.
- [05] C2PA. FAQs and Content Credentials Explainer.
- [06] Adobe. Content Credentials overview.
- [07] Google DeepMind. SynthID and SynthID Detector.
- [08] CISA / JCDC. AI Cybersecurity Collaboration Playbook.